The upstream build of the fuzzer currently builds freetype --without-zlib and --without-png so these are not needed. In addition, because of the way these dependencies are used they must be built with the sanitizer in order to detect interesting issues like CVE-2020-15999, where FreeType may call into libpng incorrectly but it is libpng which actually does the reads and writes. This has been proposed upstream at https://github.com/freetype/freetype2-testing/pull/86 which uses prefixes to ensure that the system symbols are never used, but it would be beneficial to not have them available at all. |
||
|---|---|---|
| .github/workflows | ||
| docs | ||
| infra | ||
| projects | ||
| .dockerignore | ||
| .gitignore | ||
| .pylintrc | ||
| .style.yapf | ||
| CONTRIBUTING.md | ||
| LICENSE | ||
| README.md | ||
| oss-fuzz.iml | ||
README.md
OSS-Fuzz: Continuous Fuzzing for Open Source Software
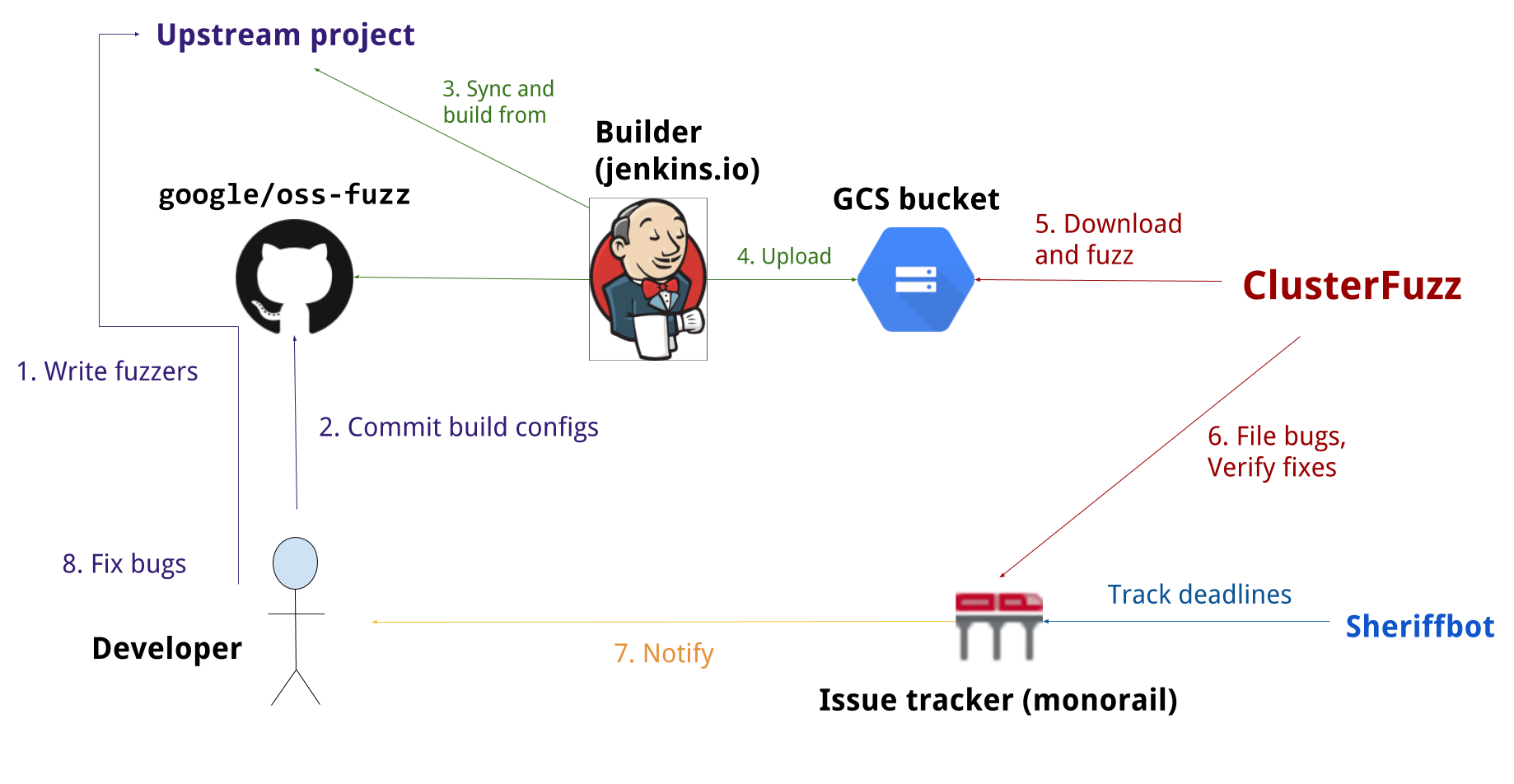
Fuzz testing is a well-known technique for uncovering programming errors in software. Many of these detectable errors, like buffer overflow, can have serious security implications. Google has found thousands of security vulnerabilities and stability bugs by deploying guided in-process fuzzing of Chrome components, and we now want to share that service with the open source community.
In cooperation with the Core Infrastructure Initiative, OSS-Fuzz aims to make common open source software more secure and stable by combining modern fuzzing techniques with scalable, distributed execution.
We support the libFuzzer, AFL, and Honggfuzz fuzzing engines in combination with Sanitizers, as well as ClusterFuzz, a distributed fuzzer execution environment and reporting tool.
Currently, OSS-Fuzz supports C/C++, Rust, and Go code. Other languages supported by LLVM may work too. OSS-Fuzz supports fuzzing x86_64 and i386 builds.
Overview
Documentation
Read our detailed documentation to learn how to use OSS-Fuzz.
Trophies
As of June 2020, OSS-Fuzz has found over 20,000 bugs in 300 open source projects.
Blog posts
- 2016-12-01 - Announcing OSS-Fuzz: Continuous fuzzing for open source software
- 2017-05-08 - OSS-Fuzz: Five months later, and rewarding projects
- 2018-11-06 - A New Chapter for OSS-Fuzz