The certificate of https://gmplib.org/ has expired. The website displays the following message: ``` YES, THE CERTIFICATE IS EXPIRED. Sorry about that. We're working on the renewal process. Unfortunately, our SSL provider changes the renewal interface each year, and it is always a challenge to figure out what to do. Now the only actions are REGENERATE (actiually not, as the cert is expired), REVOKE (well, not desirable) and INTERMEDIATE CERTIFICATE (which is not an action but a thing, oh well. ``` But this is breaking a lot of builds and this still hasn't been fixed after a few days, so with this PR I'm instead downloading the libgmp source archive and bypass the certificate check and manually verify the sha256 hash of the downloaded file. Only the `cryptofuzz` and `bignum-fuzzer` projects ideally need to use the latest repository checkout, instead of a versioned source archive, because with these projects the aim is to find bugs in libgmp. In all other projects, libgmp only serves as an oracle, and using the latest stable version is fine. Once gmp fixes their certificate, I will revert `cryptofuzz` and `bignum-fuzzer` to use the repository again. For now it's ok to use the latest stable version. |
||
|---|---|---|
| .allstar | ||
| .clusterfuzzlite | ||
| .github | ||
| docs | ||
| infra | ||
| projects | ||
| .dockerignore | ||
| .gitattributes | ||
| .gitignore | ||
| .pylintrc | ||
| .style.yapf | ||
| CONTRIBUTING.md | ||
| LICENSE | ||
| README.md | ||
README.md
OSS-Fuzz: Continuous Fuzzing for Open Source Software
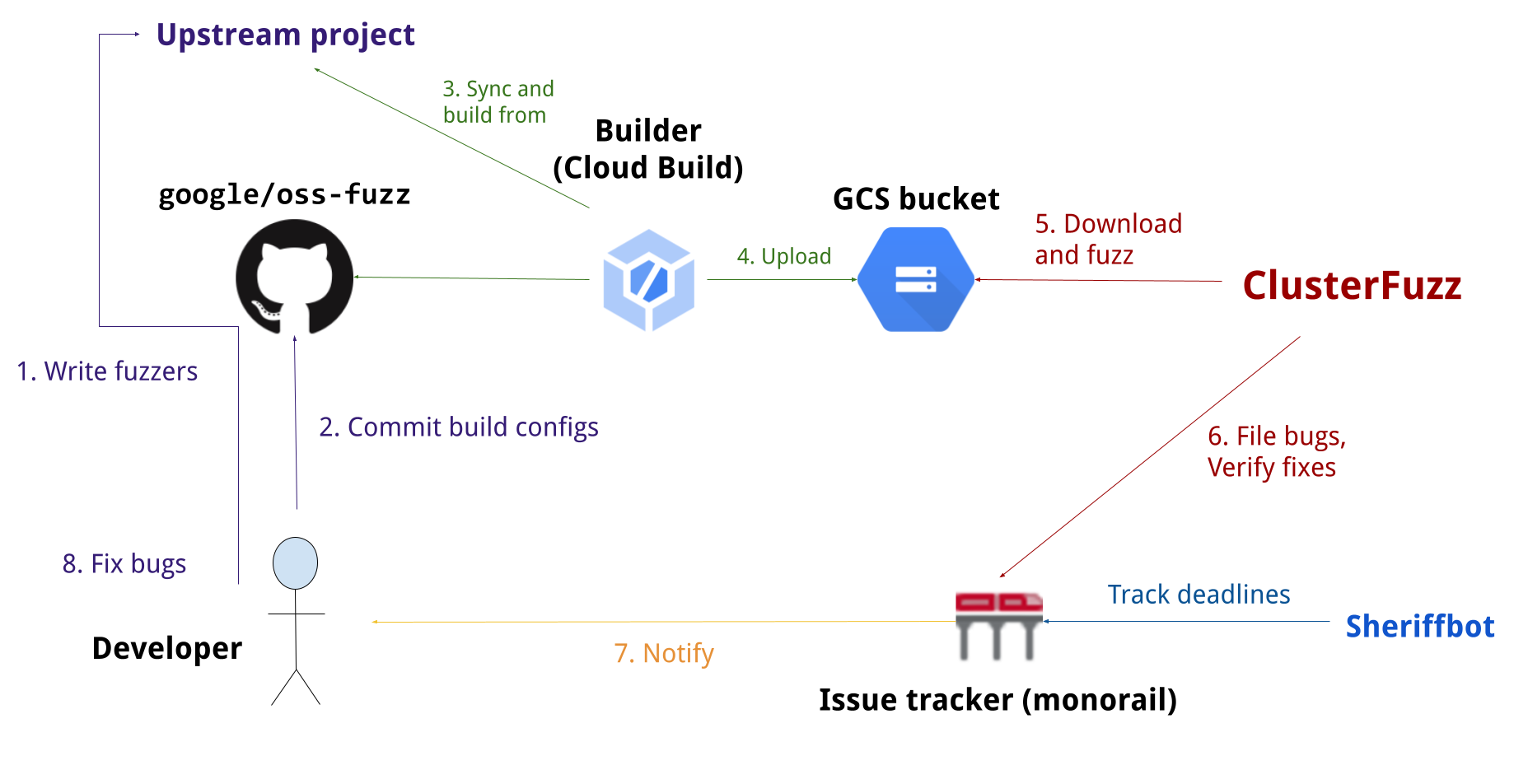
Fuzz testing is a well-known technique for uncovering programming errors in software. Many of these detectable errors, like buffer overflow, can have serious security implications. Google has found thousands of security vulnerabilities and stability bugs by deploying guided in-process fuzzing of Chrome components, and we now want to share that service with the open source community.
In cooperation with the Core Infrastructure Initiative and the OpenSSF, OSS-Fuzz aims to make common open source software more secure and stable by combining modern fuzzing techniques with scalable, distributed execution. Projects that do not qualify for OSS-Fuzz (e.g. closed source) can run their own instances of ClusterFuzz or ClusterFuzzLite.
We support the libFuzzer, AFL++, and Honggfuzz fuzzing engines in combination with Sanitizers, as well as ClusterFuzz, a distributed fuzzer execution environment and reporting tool.
Currently, OSS-Fuzz supports C/C++, Rust, Go, Python and Java/JVM code. Other languages supported by LLVM may work too. OSS-Fuzz supports fuzzing x86_64 and i386 builds.
Overview
Documentation
Read our detailed documentation to learn how to use OSS-Fuzz.
Trophies
As of July 2022, OSS-Fuzz has found over 40,500 bugs in 650 open source projects.
Blog posts
- 2016-12-01 - Announcing OSS-Fuzz: Continuous fuzzing for open source software
- 2017-05-08 - OSS-Fuzz: Five months later, and rewarding projects
- 2018-11-06 - A New Chapter for OSS-Fuzz
- 2020-10-09 - Fuzzing internships for Open Source Software
- 2020-12-07 - Improving open source security during the Google summer internship program