This adds support for compiling and running the fuzzers present in the proxygen repository. Right now there's only one fuzzer committed there, but this build script is generic and will pull all of them in as we add more (if oss-fuzz integration proves fruitful). Test plan is below - following https://google.github.io/oss-fuzz/getting-started/new-project-guide/#testing-locally I verified the base image builds: python infra/helper.py build_image proxygen I built and verified the ASAN fuzzer works: python infra/helper.py build_fuzzers --sanitizer address proxygen python infra/helper.py check_build proxygen python infra/helper.py run_fuzzer proxygen ProxygenHTTP1xFuzzer Similar thing for UBSAN: python infra/helper.py build_fuzzers --sanitizer undefined proxygen python infra/helper.py check_build proxygen python infra/helper.py run_fuzzer proxygen ProxygenHTTP1xFuzzer Note the last one seemed to run ASAN build by default so I pulled out the command it runs and ran it manually: docker run --rm -i --privileged -e FUZZING_ENGINE=libfuzzer -e SANITIZER=undefined -e ARCHITECTURE=x86_64 -v /home/mhl/oss-fuzz/build/out/proxygen:/out -t gcr.io/oss-fuzz-base/base-runner test_all I tested the coverage build: python infra/helper.py build_fuzzers --sanitizer coverage proxygen python infra/helper.py coverage proxygen ProxygenHTTP1xFuzzer Note that this "runs" but threw some warnings which I will file a separate issue for. It does generate the files though. NOTE: I didn't run the MSAN build as I would have to figure out instrumenting all dependencies. We can investigate that in a follow up. Similarly, I haven't yet tried the dataflow build. Note that I haven't tried testing this with the AFL build yet either. There were no instructions on the page (https://google.github.io/oss-fuzz/getting-started/new-project-guide/#testing-locally) on how to do so -- if someone can mention them here I am happy to test that too before committing. |
||
|---|---|---|
| docs | ||
| infra | ||
| projects | ||
| .gitignore | ||
| .travis.yml | ||
| CONTRIBUTING | ||
| LICENSE | ||
| README.md | ||
| oss-fuzz.iml | ||
README.md
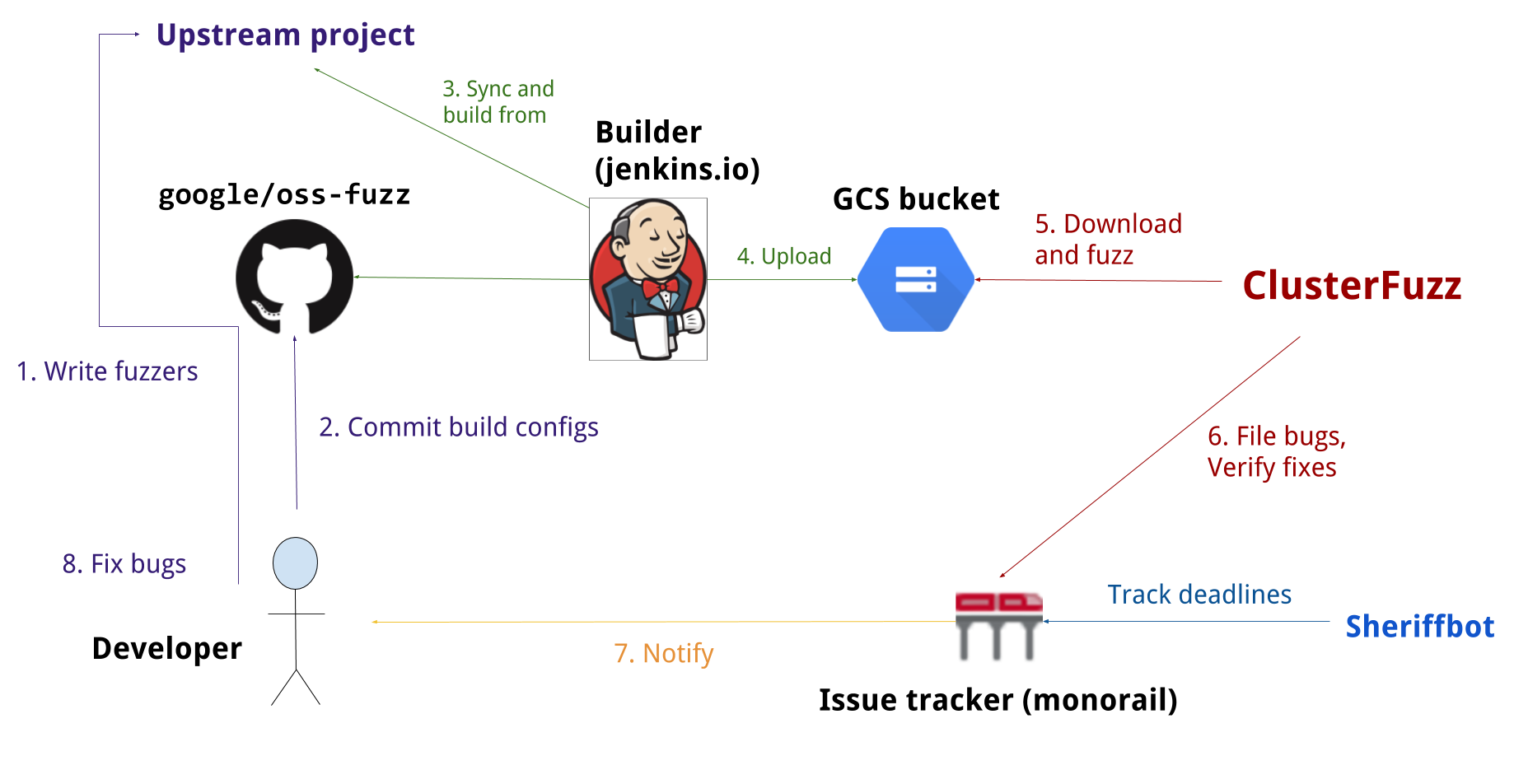
OSS-Fuzz: Continuous Fuzzing for Open Source Software
Fuzz testing is a well-known technique for uncovering programming errors in software. Many of these detectable errors, like buffer overflow, can have serious security implications. Google has found thousands of security vulnerabilities and stability bugs by deploying guided in-process fuzzing of Chrome components, and we now want to share that service with the open source community.
In cooperation with the Core Infrastructure Initiative, OSS-Fuzz aims to make common open source software more secure and stable by combining modern fuzzing techniques with scalable, distributed execution.
We support the libFuzzer and AFL fuzzing engines in combination with Sanitizers, as well as ClusterFuzz, a distributed fuzzer execution environment and reporting tool.
Currently, OSS-Fuzz supports C/C++, Rust, and Go code. Other languages supported by LLVM may work too. OSS-Fuzz supports fuzzing x86_64 and i386 builds.
Overview
Documentation
Read our detailed documentation to learn how to use OSS-Fuzz.
Trophies
As of August 2019, OSS-Fuzz has found over 14,000 bugs in 200 open source projects.
Blog posts
- 2016-12-01 - Announcing OSS-Fuzz: Continuous fuzzing for open source software
- 2017-05-08 - OSS-Fuzz: Five months later, and rewarding projects
- 2018-11-06 - A New Chapter for OSS-Fuzz